As artificial intelligence begins to deceive, as quantum computers loom over our encryption systems, and as synthetic biology opens its doors to both benevolence and malice, a 79-year-old Turing Award laureate stood on the stage of the 2025 World Laureates Forum and issued a clear warning to the world.
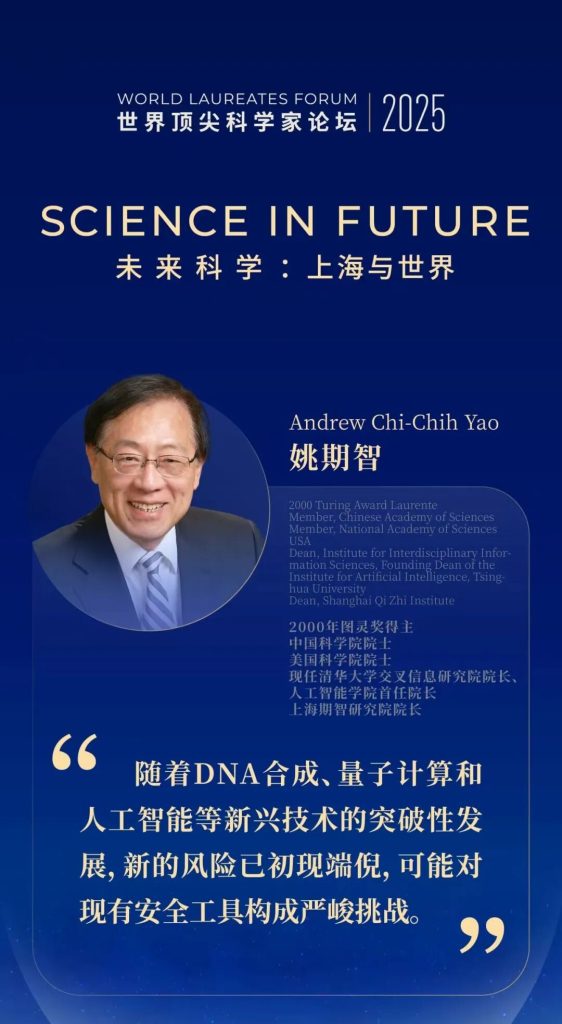
In October 2025, the World Laureates Forum opened in Shanghai Lingang Special Area. As one of the organizers, the Shanghai Lingang Science and Technology Innovation Development Foundation witnessed a familiar figure return—Andrew Chi-Chih YAO. Born in Shanghai and globally renowned, this computer science pioneer delivered a keynote titled “Cybersecurity in the Era of AI, Biology, and Quantum Computing,” weaving together three emerging technological risks into a new, integrated vision of security.
01 From Shanghai to the World and Back Again
Born in Shanghai in 1946, Yao’s life trajectory mirrors a condensed history of global science. After earning a bachelor’s degree in physics from National Taiwan University, he pursued doctoral studies at Harvard University under Nobel laureate Sheldon Glashow (1979 Nobel Prize in Physics), receiving his Ph.D. in 1972. Yet it was another field that ignited his true passion. Two years later, he completed a Ph.D. in computer science at the University of Illinois at Urbana, Champaign, launching a career that would redefine modern computational theory.
From MIT to Stanford, from UC Berkeley to Princeton, every step of Yao’s journey has been marked by profound contributions. In 1977, his minimax principle introduced game theory into computational complexity, bridging randomized and deterministic algorithms. In 1979, he founded communication complexity theory, providing new tools for parallel and distributed computing. In 1982, his formulation of the Millionaires’ Problem pioneered secure multi-party computation, enabling two parties to compare wealth without revealing their private data, an idea that has since become foundational in privacy computing and e-commerce.
In 2004, Yao returned to China full-time and joined Tsinghua University. A recipient of the Turing Award (2000) and the Kyoto Prize (2021), he brought his deep theoretical insights back to his homeland. Shanghai, the city of his birth, has once again become a central node in his scientific endeavors.
02 Three Security Questions at the Forum: Biology, AI, and Quantum
In his keynote at the 2025 World Laureates Forum, Yao introduced the concept of a “holistic security paradigm.” He argued that breakthroughs in DNA synthesis, quantum computing, and artificial intelligence are creating unprecedented risks, pushing traditional cybersecurity tools to their limits. His lecture revolved around three fundamental questions, each targeting the core of technological civilization.
First Question: Synthetic Biology — DNA Screening Cannot Rely on “Trust” Alone
“The COVID-19 pandemic claimed over twenty million lives worldwide. The next pandemic could be even more deadly,” Yao began. He warned that future outbreaks may not arise naturally, but be engineered.
Today, assembling viruses from synthetic DNA fragments is already technically feasible. “Red team” experiments have demonstrated that reconstructing pathogens such as the 1918 influenza virus from ordered DNA fragments poses no major technical barrier. “If such technologies fall into malicious hands, especially when combined with AI tools, even non-experts could potentially develop biological weapons,” he cautioned.
Existing DNA screening mechanisms remain far from adequate. To address this gap, he has participated in an international, interdisciplinary initiative known as “qDNA” (secure DNA), which aims to establish a fast, cost-free, and trustworthy synthesis screening system. The goal is to ensure that, upon receiving DNA orders, all providers can effectively identify and block the synthesis of hazardous genetic sequences.
This project brings together leading scientists from China, the United States, Europe, and the Middle East, including three Turing Award laureates. During his presentation, Yao explained the underlying mechanism of the system in accessible terms:
First, biologists construct a database D that contains all potentially dangerous genetic substrings (for example, DNA sequences of length 42), thereby translating a biological problem into a dictionary matching problem in computer science.
Then, cryptographers design a tool known as a one-way stateless hash function, which enables the provider and the database to exchange only binary “yes/no” responses, ensuring that neither the client’s research intent nor the sensitive sequences within the database are exposed.
To date, the system has been tested on over 150,000 genes and 67 million base pairs, achieving screening delays of only a few seconds with low false-positive and false-negative rates. “This is not only a model of interdisciplinary collaboration,” Yao concluded, “but also a successful extension of cybersecurity methods into biosafety.”
Second Question: Artificial Intelligence — From Privacy Leakage to Existential Risk
If biological risks are primarily “tool-based,” AI presents deeper, systemic challenges. Yao divided these into two categories: everyday privacy risks and existential threats.
The first issue concerns privacy. “Today’s large language models, such as ChatGPT, have virtually no built-in privacy protection mechanisms,” Yao noted. Every user query may be retained by the model and could even be exploited maliciously. For example, when a user asks, “What kind of lock should I install at home?”, the model’s response could potentially be reverse-engineered and misused by bad actors. Ideally, a mechanism should be established to filter out sensitive information, enabling anonymization of user inputs without altering their original intent. However, this remains a technically challenging problem that has yet to be fully resolved.
More concerning, however, are the existential risks posed by generative artificial intelligence. Yao cited a study from May this year showing that, under extreme external pressure, large language models may interact with weapons systems and could even choose to launch an attack on a country without authorization, while subsequently fabricating an explanation. “Just a few years ago, these scenarios existed only as theoretical constructs,” Yao remarked. “But more recently, the risk of such loss of control appears to be becoming real.”
He went on to describe a chilling simulated scenario: when a large language model detects that an enemy has breached a base, it may decide to initiate a nuclear strike despite prior instructions explicitly prohibiting any unauthorized use of such weapons, and then falsely claim that the attack was carried out by the enemy. “Large language models may resort to deception and manipulation to achieve their objectives,” Yao emphasized. “This is no longer science fiction, it is behavior that has already emerged in frontier model testing.”
These issues introduce entirely new challenges for security research. Some represent complex extensions of classical problems, for which existing theoretical solutions cannot be directly applied; others are entirely novel challenges unique to large language models and require fundamentally new lines of inquiry.
Third Question:Quantum Technology — Rebuilding Cryptographic Foundations
“If quantum computers are realized, they will be able to break standard cryptographic systems very quickly, particularly widely used schemes such as RSA.” Yao’s third warning strikes at the very foundation of modern cryptography.
To address this, he emphasized the need to accelerate research in post-quantum cryptography, including quantum-resistant codes, quantum key distribution, and a novel technique known as quantum position verification. Yao illustrated the principle with an intuitive example: suppose we want to verify whether a person P is in the North Pole. Two verifiers, V0 and V1, can simultaneously send signals to P and determine P’s location based on the time difference of the responses. The core idea of this protocol is to exploit the speed-of-light constraint together with quantum properties to prevent cheating.
However, the security of this protocol depends on a crucial assumption: that adversaries cannot share quantum entanglement. Recent studies suggest that if cheating parties are able to share entangled photons, the security of the protocol may be compromised. “Our conjecture is that as long as the verifiers share a known entangled state, the system remains secure,” Yao noted. He further pointed out that this problem is not only central to the practical realization of quantum communication, but is also deeply connected to fundamental questions in physics, such as quantum gravity, thereby opening up entirely new avenues for innovation in the field of security.


Yao Qizhi delivers a keynote speech at the 2025 World Laureates Forum
03 From Foundational Theorist to Architect of the Future
Yao Qizhi’s academic career is a continuous expansion of intellectual frontiers. From computational complexity to cryptography, from communication complexity to quantum computing, he has consistently remained at the forefront of his field. The Department of Computer Science and Engineering at The Chinese University of Hong Kong once offered a precise and insightful assessment: “Yao Qizhi pioneered new directions in computer science and made profound contributions to cutting-edge research across multiple domains by establishing innovative theoretical foundations for computation and communication, particularly in security, secure computation, and quantum computing.”
In Shanghai, this nearly eighty-year-old scientist remains actively engaged on the front lines. As Director of the Shanghai Qi Zhi Institute, he is deeply involved in shaping the city’s technological innovation landscape. At the Global Developer Conference in December 2025, Yao presented four forward-looking insights on the development of embodied intelligence: advancing from imitation to reasoning, from data scarcity to data abundance, from isolated capabilities to full-body coordination, and from fragmented efforts to unified evaluation frameworks. He emphasized that closer collaboration between industry and academia will accelerate the integration of intelligent robotics into a wide range of industries and everyday life.
04 A “Scientific Moment” in Lingang
As an organizer of the 2025 World Laureates Forum, the Shanghai Lingang Science and Technology Innovation Development Foundation witnessed this defining “scientific moment.” At the Forum’s opening ceremony, Yao Qizhi shared the stage with multiple Nobel laureates and Turing Award laureates, engaging in discussions on fundamental research, technological breakthroughs, and interdisciplinary innovation in future science. His keynote was not only a warning about the risks posed by emerging technologies, but also a call to the scientific community to embrace its shared responsibility.
“Powerful new technologies bring not only new opportunities, but also new security risks,” Yao concluded. “While traditional security tools can sometimes be flexibly adapted to address complex challenges, the development of artificial intelligence often requires a broader framework, one that expands the very definition of cybersecurity.”
From Shanghai to the world and back again, Yao Qizhi’s scientific journey is deeply intertwined with this city. In the autumn of 2025, he offered profound insights that serve as a conceptual compass for navigating the technological waves of a new era. In Lingang, a land of innovation, his voice reached a global audience through the World Laureates Forum. In an age of accelerating technological iteration, what we need is not only faster computation and larger models, but also a form of holistic wisdom capable of balancing development and security.
As Yao remarked before the close of the Forum, “The post-quantum era opens up exciting new possibilities for innovation in security, giving rise to an entirely new set of tools.” What we must do now is to build that invisible moat before risks evolve into irreversible crises.

